HUMINT (Human Intelligence)
Brief historical view
HUMINT primarily relied on traditional espionage and in-person human interactions, along with physical document handling. Field operatives and case officers used common practices to establish and maintain networks of assets (informants) in target regions. These officers were trained in clandestine operations, tradecraft, and counter-surveillance techniques.
Establishing trust with assets necessitated a substantial investment of time and resources. Operatives frequently spent years undercover in a region to acquire valuable information. Information was often exchanged through face-to-face meetings or physical methods such as dead drops (concealed locations for leaving messages or items). Communications with assets were meticulously managed to evade detection, and meetings necessitated sophisticated counter-surveillance to prevent exposing the asset or officer.
A substantial emphasis was placed on gathering intelligence from hostile nations and governments.
Intelligence gathering primarily targeted traditional state actors, military secrets, and political developments, particularly in regions such as the Middle East and Eastern Europe, which were perceived as high-risk geopolitical zones. The primary targets of this intelligence-gathering effort were government officials, diplomats, military personnel, and defectors.
Technology support was limited, necessitating a heavy reliance on face-to-face communication. Digital communication and remote handling were less secure due to these constraints. Surveillance equipment, such as micro-cameras and recording devices, was utilized sparingly due to its limited availability and heightened risk of detection.
In conflict zones, interrogations and direct questioning were the primary methods of gathering intelligence. Prisoners of war, defectors, or suspected agents were commonly interrogated to extract critical information.
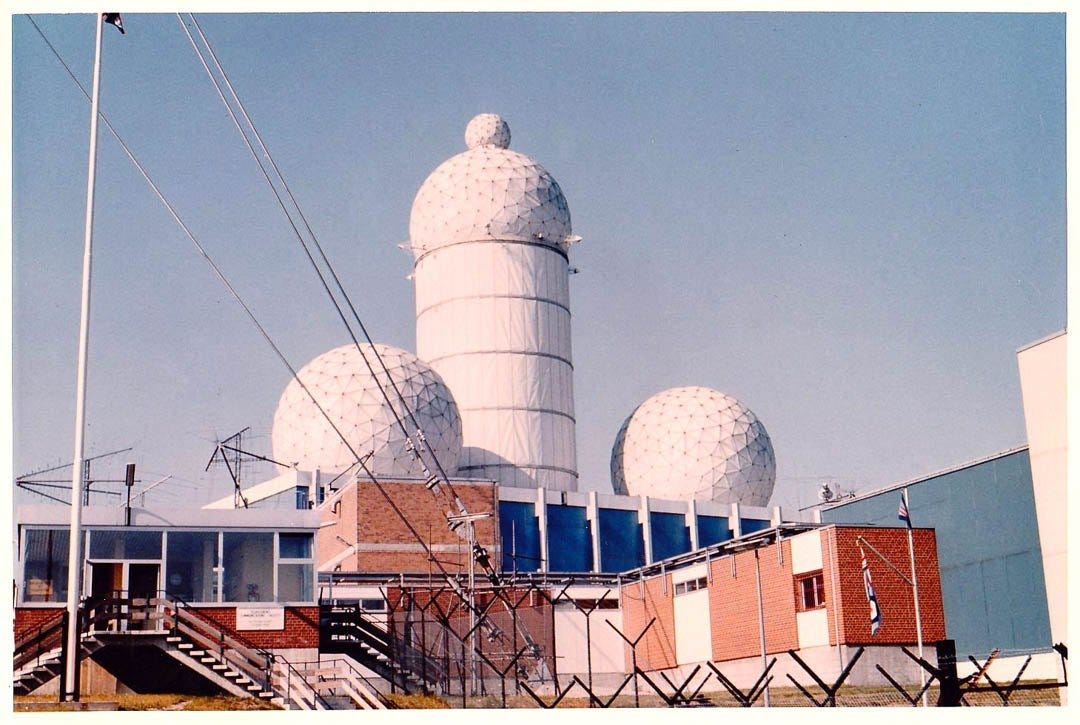
The two pictures show the outpost of the US as far east as possible in West Berlin’s Teufelsberg in the fifties.
The surveillance station was tasked with the most sophisticated equipment available at the time to listen to communication, analyze in various languages and communicate constantly the findings to US military as well as to data collection agencies including the NSA. More than 100 people were onsite during regular operations.
In the context of technological advancements and a shifting global landscape, modern human intelligence (HUMINT) has evolved to embrace novel tools and adapt to the evolving behavior of targets. HUMINT increasingly utilizes encrypted digital communication to recruit and manage assets remotely, often bypassing the necessity for direct contact. Secure messaging applications, encrypted emails, and specialized communication software facilitate interactions with sources across borders.
Digital identities and online aliases (also referred to as “cyber personas”) are frequently employed to engage with potential sources, particularly in regions where physical presence poses risks. Social media platforms provide valuable data for HUMINT operations, enabling agents to monitor targets’ activities, recruit assets, and conduct background checks online.
Broader reading about many other methods in my book:
“Data Collection and Analysis in Hostile Environments”
https://technicspub.com/data-collection-and-analysis/